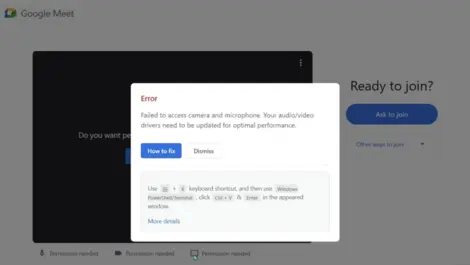
Malware represents a broad category of malicious software designed to infiltrate, damage, or disrupt computer systems and networks. From ransomware that locks users out of their data to spyware that quietly steals information, malware continues to evolve in sophistication and reach. Our recent stories cover a wide range of malware threats impacting individuals, businesses, and critical infrastructure, illustrating the diverse strategies cybercriminals use to exploit vulnerabilities.
Delving into these stories provides readers with insights into how malware campaigns operate, the latest trends in attack vectors, and expert advice on defense mechanisms. Understanding malware not only alerts individuals and organisations to potential risks but also guides them in strengthening their digital security posture. Stay informed about the ever-changing malware landscape to better safeguard your data and systems from emerging cyber threats.